Tag Archive: hacker
Learn to Fight Cyber Crime with the Cyber Ethical Hacker eLearning Bundle – only $23!
NOW ON: Learn to Fight Cyber Crime with the Cyber Ethical Hacker eLearning Bundle – only $23!
Expires: July 5, 2018, 11:59 pm EST

In the last 24 months alone we saw massive cybersecurity attacks on Uber, Deloitte and Equifax to name just a few. With a substantial shortage of qualified cyber crime fighters around the globe, demand for cybersecurity professionals is higher than ever. With this Cyber Ethical Hacker eLearning Bundle from AcademyHacker.com, you’ll learn be trained in a variety of tools to help you recognize and beat hackers.
Highlights:
- 20 courses filling more than 90 hours.
- Lifetime access to online courses.
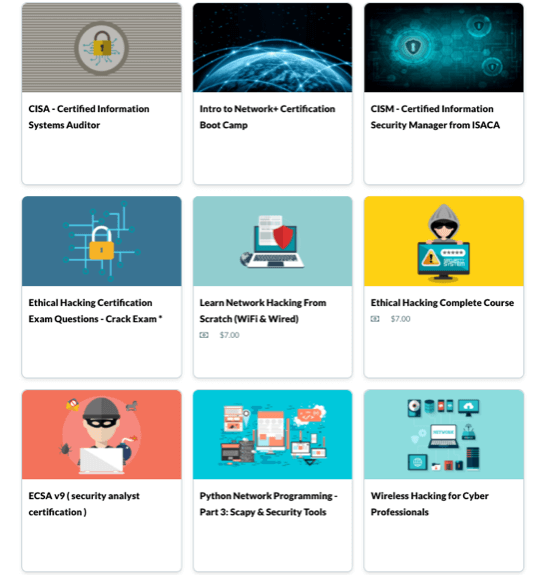
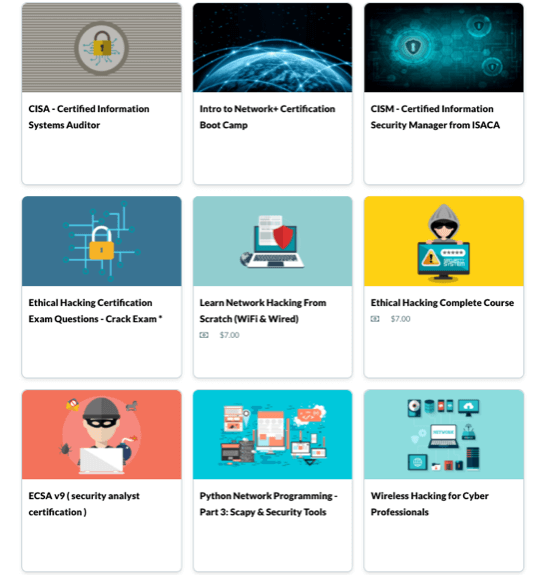
- Become a cyber crime fighter through dozens of courses – ethical hacking, security certification, python network programming, Certified Information Systems Auditor and more.

Testimonials:
“Concepts are well explained and instructor takes the effort to put some of them in layman terms for easy understanding” – Ryan
“This is an awesome course. I am a fan of Mr Zaid! He is doing practical classes rather than theory. I don’t feel bored during his courses at all.” – Shane
Pricing:
Normally this online course collection sells for $199 but for a limited time only you can get a lifetime access to the Cyber Ethical Hacker eLearning Bundle for just $23. That’s a massive savings of 88% off the regular price.
Click the BUY NOW button to start fighting cyber crime today!
Deal terms:
- You’ll receive a coupon code after completing your purchase, to register at the AcademyHacker website for lifetime access.
- All videos are streamable downloads and require an Internet connection for viewing. They are not downloadable.
Learn to Fight Cyber Crime with the Cyber Ethical Hacker eLearning Bundle – only $23!
NOW ON: Learn to Fight Cyber Crime with the Cyber Ethical Hacker eLearning Bundle – only $23!
Expires: July 24, 2018, 11:59 pm EST

In the last 24 months alone we saw massive cybersecurity attacks on Uber, Deloitte and Equifax to name just a few. With a substantial shortage of qualified cyber crime fighters around the globe, demand for cybersecurity professionals is higher than ever. With this Cyber Ethical Hacker eLearning Bundle from AcademyHacker.com, you’ll learn be trained in a variety of tools to help you recognize and beat hackers.
Highlights:
- 20 courses filling more than 90 hours.
- Lifetime access to online courses.
- Become a cyber crime fighter through dozens of courses – ethical hacking, security certification, python network programming, Certified Information Systems Auditor and more.

Testimonials:
“Concepts are well explained and instructor takes the effort to put some of them in layman terms for easy understanding” – Ryan
“This is an awesome course. I am a fan of Mr Zaid! He is doing practical classes rather than theory. I don’t feel bored during his courses at all.” – Shane
Pricing:
Normally this online course collection sells for $199 but for a limited time only you can get a lifetime access to the Cyber Ethical Hacker eLearning Bundle for just $23. That’s a massive savings of 88% off the regular price.
Click the BUY NOW button to start fighting cyber crime today!
Deal terms:
- You’ll receive a coupon code after completing your purchase, to register at the AcademyHacker website for lifetime access.
- All videos are streamable downloads and require an Internet connection for viewing. They are not downloadable.

The Ethical Hacker Bootcamp Bundle for $39

KEY FEATURES
Hackers are getting more sophisticated by the day, but so are their crime-fighting counterparts. Commonly known as ethical hackers, these cybersecurity experts leverage a hacker’s own tools against them, keeping networks—and the sensitive data they hold—safe. Featuring more than 75 hours of training, this collection of expert-led courses can help you take the fight online and certify your skills as a bona fide cybersecurity professional.
- Access 526 lessons & 77 hours of content 24/7
- Learn from industry experts in an interactive, lab-filled environment
- Foster skills in incident management, penetration testing & more
- Explore common threats, such as viruses, social engineering & DDoS attacks
- Understand the necessary steps to secure a system
- Prepare to ace the EC-Council Certified Ethical Hacker v9 exam upon completion
Included Courses:
- Introduction to Ethical Hacking
- Footprinting and Reconnaissance
- Scanning Networks
- Enumeration
- Malware Threats
- Sniffing
- Social Engineering
- Denial of Service
- System Hacking
- Session Hijacking
- Hacking Webservers
- Hacking Web Applications
- SQL Injection
- Hacking Wireless Networks
- Hacking Mobile Platforms
- Evading IDS, Firewalls, and Honeypots
- Cloud Computing
- Cryptography
- CEH – Test Prep Questions
PRODUCT SPECS
Details & Requirements
- Length of time users can access this content: 1 year
- Access options: web
- Certification of completion included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: all levels
Compatibility
- Internet required
THE EXPERT
CyberTraining 365 is the best training destination for you and your team. Here you can Master Cyber Security techniques such as Analyzing Malware, Penetration Testing, Advanced Persistent Threats, Threat Intelligence Research, Reverse Engineering, and much more.
The training courses are up-to-date on all the latest technologies and industry standards. All of this is offered at a great value in a self-paced online environment. CyberTraining 365 prepares you for industry-recognized certifications so you are fully prepared for the best job opportunities in the industry.

Zero to Hero Cyber Security Hacker Bundle for $29

KEY FEATURES
In this course, you’ll learn how viruses, worms, Trojans, and backdoor-based attacks are performed in a simulated test environment in an ethical way. It has been designed to enable you to learn core concepts on malware and become familiar with how various types of attacks are performed. Ultimately, you will come out fully prepared to test and safeguard a system against various real-time attack vectors.
- Access 37 lectures & 1 hour of content 24/7
- Cover the ground basics about malware
- Develop your skills in the field of internet security
- Learn how to perform various types of malware hacks
- Understand how to mitigate against these types of attacks
- Accelerate your learning process through the use of creative animations & easy to understand voice over narratives
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: lifetime
- Access options: web streaming, mobile streaming
- Certification of completion not included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: all levels
Compatibility
- Internet required
THE EXPERT
Vinod Senthil is the Founder & CTO of infySEC. Vinod is passionate about application building, debugging, disassembling computers, compiling, and much more. Over time he has developed interests in networking and, eventually, networking security.
After 14 years of experience, Vinod has turned his efforts to teaching people how attackers hack systems so they may understand how to secure themselves and other from attack. His instruction is actionable and hands-on, with live demos and lab exercises that will allow you to implement what you have learned immediately.
In 2013, Vinod, along with his team at infySEC, set the world record for conducting the largest and longest ethical hacking marathon with over 9,000 participants assembled in one location.

KEY FEATURES
In this course, you’ll learn how cryptography, steganography, password cracking, game hacking, reverse engineering, and privilege escalation based attacks are performed in a simulated test environment in an ethical way. This course helps system security professionals mitigate these attacks. It’s perfect for anybody who is passionate about developing their skills in the field of internet security.
- Access 50 lectures & 2 hours of content 24/7
- Cover the ground basics about systems
- Learn how to perform various types of system hacks
- Understand how to mitigate against these types of attacks
- Accelerate your learning process through the use of creative animations & easy to understand voice over narratives
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: lifetime
- Access options: web streaming, mobile streaming
- Certification of completion not included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: advanced
Compatibility
- Internet required
THE EXPERT
Vinod Senthil is the Founder & CTO of infySEC. Vinod is passionate about application building, debugging, disassembling computers, compiling, and much more. Over time he has developed interests in networking and, eventually, networking security.
After 14 years of experience, Vinod has turned his efforts to teaching people how attackers hack systems so they may understand how to secure themselves and other from attack. His instruction is actionable and hands-on, with live demos and lab exercises that will allow you to implement what you have learned immediately.
In 2013, Vinod, along with his team at infySEC, set the world record for conducting the largest and longest ethical hacking marathon with over 9,000 participants assembled in one location.

KEY FEATURES
In this course, you’ll learn how client-based, server-based, and application-based web attacks are performed in a simulated test environment in an ethical way, at an advanced level. This course helps the web security professional to mitigate these attacks using the recommended solution at the end of each module. By course’s end, you’ll be familiar with various types of web hacks and be fully equipped to test and safeguard a web infrastructure against various real-time attack vectors.
- Access 28 lectures & 2 hours of content 24/7
- Learn how to perform advanced client-based, server-based, & application-based web attacks
- Understand how to mitigate against these types of attacks
- Accelerate your learning process through the use of creative animations & easy to understand voice over narratives
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: lifetime
- Access options: web streaming, mobile streaming
- Certification of completion not included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: advanced
Compatibility
- Internet required
THE EXPERT
Vinod Senthil is the Founder & CTO of infySEC. Vinod is passionate about application building, debugging, disassembling computers, compiling, and much more. Over time he has developed interests in networking and, eventually, networking security.
After 14 years of experience, Vinod has turned his efforts to teaching people how attackers hack systems so they may understand how to secure themselves and other from attack. His instruction is actionable and hands-on, with live demos and lab exercises that will allow you to implement what you have learned immediately.
In 2013, Vinod, along with his team at infySEC, set the world record for conducting the largest and longest ethical hacking marathon with over 9,000 participants assembled in one location.

KEY FEATURES
In this course, you’ll learn how wired and wireless network attacks are performed in a simulated test environment in an ethical way. This course helps the network security professional to mitigate each of these attacks. By course’s end, you’ll be well equipped to test and safeguard network infrastructure against attack.
- Access 59 lectures & 2 hours of content 24/7
- Cover ground basics about the web
- Learn how to perform various types of network hacks
- Understand how to mitigate against these types of attacks
- Accelerate your learning process through the use of creative animations & easy to understand voice over narratives
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: lifetime
- Access options: web streaming, mobile streaming
- Certification of completion not included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: intermediate
Compatibility
- Internet required
THE EXPERT
Vinod Senthil is the Founder & CTO of infySEC. Vinod is passionate about application building, debugging, disassembling computers, compiling, and much more. Over time he has developed interests in networking and, eventually, networking security.
After 14 years of experience, Vinod has turned his efforts to teaching people how attackers hack systems so they may understand how to secure themselves and other from attack. His instruction is actionable and hands-on, with live demos and lab exercises that will allow you to implement what you have learned immediately.
In 2013, Vinod, along with his team at infySEC, set the world record for conducting the largest and longest ethical hacking marathon with over 9,000 participants assembled in one location.

KEY FEATURES
Have you ever wanted to learn computer hacking and become a real-life cyber warrior for the good guys, then this is the place to be. This is a great opportunity for security enthusiasts and ethical hackers to learn hacking fundamentals through live demonstrations and hands-on experience with the latest tools.
- Access 49 lectures & 2 hours of content 24/7
- Learn about real-time attack vectors & defensive methods
- Gain a deep understanding of how attackers work
- Understand how to secure your systems from hackers
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: lifetime
- Access options: web streaming, mobile streaming
- Certification of completion not included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: beginner
Compatibility
- Internet required
THE EXPERT
Vinod Senthil is the Founder & CTO of infySEC. Vinod is passionate about application building, debugging, disassembling computers, compiling, and much more. Over time he has developed interests in networking and, eventually, networking security.
After 14 years of experience, Vinod has turned his efforts to teaching people how attackers hack systems so they may understand how to secure themselves and other from attack. His instruction is actionable and hands-on, with live demos and lab exercises that will allow you to implement what you have learned immediately.
In 2013, Vinod, along with his team at infySEC, set the world record for conducting the largest and longest ethical hacking marathon with over 9,000 participants assembled in one location.

KEY FEATURES
In this course, you’ll learn how client-based, server-based, and application-based web attacks are performed in a simulated test environment in an ethical way. This course helps the web security professional to mitigate these attacks using the recommended solution at the end of each module. By course’s end, you’ll be familiar with various types of web hacks and be fully equipped to test and safeguard a web infrastructure against various real-time attack vectors.
- Access 35 lectures & 1.5 hours of content 24/7
- Learn how to perform client-based, server-based, & application-based web attacks
- Understand how to mitigate against these types of attacks
- Accelerate your learning process through the use of creative animations & easy to understand voice over narratives
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: lifetime
- Access options: web streaming, mobile streaming
- Certification of completion not included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: intermediate
Compatibility
- Internet required
THE EXPERT
Vinod Senthil is the Founder & CTO of infySEC. Vinod is passionate about application building, debugging, disassembling computers, compiling, and much more. Over time he has developed interests in networking and, eventually, networking security.
After 14 years of experience, Vinod has turned his efforts to teaching people how attackers hack systems so they may understand how to secure themselves and other from attack. His instruction is actionable and hands-on, with live demos and lab exercises that will allow you to implement what you have learned immediately.
In 2013, Vinod, along with his team at infySEC, set the world record for conducting the largest and longest ethical hacking marathon with over 9,000 participants assembled in one location.
KEY FEATURES
This course forms the basis for anyone who wants to become a real-time penetration tester. You’ll learn how to research and gather information about a target without leaving any traces, all in an ethical way. By the end of the course, you’ll be familiar with how attackers gather their information before launching an attack, and know how to mitigate it beforehand.
- Access 47 lectures & 1 hour of content 24/7
- Discuss complex hacking concepts in easily understood modules
- Develop your skills in the internet security field
- Gain familiarity w/ how attackers gather various types of information
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: lifetime
- Access options: web streaming, mobile streaming
- Certification of completion not included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: all levels
Compatibility
- Internet required
THE EXPERT
Vinod Senthil is the Founder & CTO of infySEC. Vinod is passionate about application building, debugging, disassembling computers, compiling, and much more. Over time he has developed interests in networking and, eventually, networking security.
After 14 years of experience, Vinod has turned his efforts to teaching people how attackers hack systems so they may understand how to secure themselves and other from attack. His instruction is actionable and hands-on, with live demos and lab exercises that will allow you to implement what you have learned immediately.
In 2013, Vinod, along with his team at infySEC, set the world record for conducting the largest and longest ethical hacking marathon with over 9,000 participants assembled in one location.

KEY FEATURES
The essential objective of this course is to create awareness regarding the various basic information security requirements and how these requirements can be interpreted to suit an organization’s processes, products, people, and customers. In this course, you’ll learn how employees, business owners, and other computer users tend to have their security compromised, and what you can do to help safeguard yourself and others from digital attacks.
- Access 34 lectures & 1 hour of content 24/7
- Learn what every employee of an organization can do to avoid attack
- Understand ISO 27001:2013 guidelines
- Discover how to securely handle data, media containing data, & IT devices
- Explore how various technical & non-technical attack methods are performed
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: lifetime
- Access options: web streaming, mobile streaming
- Certification of completion not included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: beginner
Compatibility
- Internet required
THE EXPERT
Vinod Senthil is the Founder & CTO of infySEC. Vinod is passionate about application building, debugging, disassembling computers, compiling, and much more. Over time he has developed interests in networking and, eventually, networking security.
After 14 years of experience, Vinod has turned his efforts to teaching people how attackers hack systems so they may understand how to secure themselves and other from attack. His instruction is actionable and hands-on, with live demos and lab exercises that will allow you to implement what you have learned immediately.
In 2013, Vinod, along with his team at infySEC, set the world record for conducting the largest and longest ethical hacking marathon with over 9,000 participants assembled in one location.
Pay What You Want: The Ultimate White Hat Hacker 2018 Bundle for $1
KEY FEATURES
Over this course you’ll learn network hacking techniques and vulnerability scanning to discover security risks across an entire network, learning skills for which companies are willing to pay top dollar. Whether you want to protect your own network or protect corporate networks professionally, this course will get you up to speed.
- Access 106 lectures & 12.5 hours of content 24/7
- Architect your network for maximum security & prevent local & remote attacks
- Understand the various types of firewalls available, including layer 4 firewalls like Iptables & PF
- Discuss firewalls on all platforms, including Windows, Mac OS, & Linux
- Explore wireless security & learn how WiFi is hacked
- Use tools like Wireshark, Tcpdump, & Syslog to monitor your network
- Dive into search engine privacy & tracking, learning how to mitigate tracking & privacy issues
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: lifetime
- Access options: web streaming, mobile streaming
- Certification of completion not included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: all levels
Compatibility
- Internet required
THE EXPERT
Nathan House has over 24 years experience in cyber security where he has advised some of largest companies in the world, assuring security on multi-million and multi-billion pound projects. He is CEO of Station X, a cyber security consultancy. More recently Nathan acted as the lead security consultant on a number of the UK’s mobile banking and payment solutions helping secure to date over £71Bn in transactions.
His clients have included; BP, ExxonMobil, Shell, Vodafone, VISA, T-mobile, GSK, COOP Banking Group, Royal Bank of Scotland, Natwest, Yorkshire bank, BG Group, BT, London 2012.
Over the years he has spoken at a number of security conferences, developed free security tools, and discovered serious security vulnerabilities in leading applications. Nathan’s qualifications and education include:
- BSc. (Hons) Computing ‘Networks & Communication’ 1st Class Honors
- SCF : SABSA Charted Architect Foundation
- CISSP : Certified Information Systems Security Professional
- CISA : Certified Information Systems Auditor
- CISM : Certified Information Security Manager
- ISO 27001 Certified ISMS Lead Auditor
- CEH : Certified Ethical Hacker
- OSCP : Offensive Security Certified Professional

KEY FEATURES
This course is focused on the practical side of penetration testing without neglecting the theory behind each attack. As you gain a complex understanding of websites, you will then learn how you can exploit them to carry out a number of powerful cyber attacks. You’ll track from a beginning to advanced level and by the time you finish you’ll be able to launch attacks and test the security of websites and apps the same way that black hat hackers would, and be able to fix these vulnerabilities.
- Access 93 lectures & 9 hours of content 24/7
- Learn how to gather information about your target site like discovering the DNS server used & subdomains
- Discover, exploit, & fix a number of vulnerabilities like file upload, code execution, SQL injection, XSS, & much more
- Understand what you can do w/ the access gained from vulnerabilities
- Explore the basic exploitation of attacks & the advanced methods to enhance them
- Learn how & why vulnerabilities are exploitable, how to fix them, & the right practices to avoid them
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: lifetime
- Access options: web streaming, mobile streaming
- Certification of completion not included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: all levels
Compatibility
- Internet required
THE EXPERT
Zaid Al-Quraishi is an ethical hacker, pentester, and programmer. He has extensive experience in ethical hacking and penetration testing, more specifically with regard to network security. Zaid started making video tutorials in 2009 for the ethical hacking website iSecuri1ty, and has also served as an editor, manager, and penetration tester for the company. He teaches mostly by example, specifically by first explaining the theory of each technique and then how it translates to a real-life situation.

KEY FEATURES
To break into the world of professional penetration testing, you’ll need to be an ace with Kali Linux. This course will introduce you to the latest ethical hacking tools and techniques with Kali Linux, using a testing lab for practicing different types of attacks. Across the course, you’ll simulate an entire penetration test from beginning to end, giving you verifiable hands-on experience.
- Access 80 lectures & 8.5 hours of content 24/7
- Get comfortable w/ Kali Linux & learn the penetration testing phases
- Manage Kali Linux HTTP & SSH services
- Discover essential tools like Netcat & WireShark
- Gather passive & active information
- Explore how to perform & defend against a variety of attacks
- Receive monthly virtual machines as a hacking challenge
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: lifetime
- Access options: web streaming, mobile streaming
- Certification of completion not included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: all levels
Compatibility
- Internet required
THE EXPERT
Mohamed Atef is an ICT Consultant, Senior Penetration tester and certified instructor with more than 20 years of experience in professional and academic courses and 2 books published.
- Certified Information System Security Professional (CISSP) ID #517943
- Microsoft Certified Trainer (MCT) ID #3022752
- EC Council Certified Instructor (CEI) ID #ECC51750391761
- CEH: Certified Ethical Hacking ID #ECC64515022319
- Certified Cisco System Instructor (CCSI)
- Microsoft Certified System Engineer (MCSE)
- Microsoft Certified IT Professional (Windows Server Administration 2008)
- CompTIA Certified (Network +) ID #
- CompTIA Certified (Server +)
- CompTIA Certified (Linux +)
- CompTIA Certified (Security +)
- Cisco Certified Network Associate (CCNA)ID #CSCO11273248
- Cisco Certified Network Professional (CCNP)
- Project Management Professional (PMP) )ID #1772374
KEY FEATURES
In this beginner- and professional-friendly course, you’ll learn how black hat hackers hack Windows using advanced techniques, while improving your knowledge on how to analyze and secure Windows, and detect a hacker’s identity. Across the example-based course, you’ll get hands-on instruction in white hat hacking.
- Access 81 lectures & 9 hours of content 24/7
- Learn how to download & setup Kali Linux 2.0, Windows 10, & Metasploit as virtual machines
- Understand how to gather as much info as possible from your target
- Use msfconsole interface like a professional
- Encode & combine the payload
- Gain full access over a target OS & learn how to interact w/ it using Meterpreter command line
- Perform various attacks over WAN network
- Detect & protect from all of the attacks discussed
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: lifetime
- Access options: web streaming, mobile streaming
- Certification of completion not included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: all levels
Compatibility
- Internet required
THE EXPERT
Saad Sarraj has been an Ethical Hacker since 2012. He founded the website iSecurityPro and has been educating people in Linux and Windows security tips through his YouTube channel over that time. He is always focused on the practical side in his teaching, and the theory behind every attack.

KEY FEATURES
This course provides a good starting point from which to learn ethical hacking and identify threats and vulnerabilities to secure your IT environment. You’ll begin with an introduction to the best tools around before diving into basic hacking technique, and ultimately going into real-life scenarios to get a hang of how hackers think.
- Access 14 lectures & 2 hours of content 24/7
- Discuss a basic introduction to reconnaissance
- Get hands-on experience working w/ Metasploit & testing the effectiveness of different defenses
- Learn about sniffing & how effective Man-in-the-Middle attacks can be
- Go through a coffee shop scenario to further your understanding
- Understand how hackers use networks to gain access to different systems
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: lifetime
- Access options: web streaming, mobile streaming
- Certification of completion not included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: all levels
Compatibility
- Internet required
THE EXPERT
Gary Dewey is an IT consultant specializing in security. A graduate of SUNY Broome’s computer security and forensics degree program in New York, he has attended numerous B-Sides conferences and spoken at B-Sides in Rochester, New York. Gary participated in the 2015 US Cyber Challenge held at Virginia Tech. He is an active member of the Triple Cities Makerspace, a non-profit organization dedicated to community collaboration and learning. He enjoys hiking and cats.
KEY FEATURES
To completely understand computer security, it’s vital to think outside the box. It’s not just about firewalls, Intrusion Prevention Systems, or antivirus. It’s also about tricking people into doing whatever a hacker wishes. A secure system, therefore, is also about informed people. This training is based on a practical approach of day-by-day situations contained labs based on real environments. The aim is to help you learn ethical hacking techniques and methodology used in penetration systems to better protect yourself and those around you.
- Access 85 lectures & 12.5 hours of content 24/7
- Cover both theoretical & practical aspects of ethical hacking
- Work in hands-on labs about hacking systems, networks, wireless, mobile, & websites
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: lifetime
- Access options: web streaming, mobile streaming
- Certification of completion not included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: all levels
Compatibility
- Internet required
THE EXPERT
Gabriel Avramescu is a Senior Information Security Consultant and IT Trainer. He works on an Internet security team focused on ethical hacking – deliberately and purposefully challenging the IT security assumptions, strategies, and methods of protecting vital assets and information by emulating an adversary.
KEY FEATURES
WAPTP v3.1 is a highly practical and hands-on training for web application penetration testing that covers the OWASP top 10 vulnerabilities. Starting with various terminologies of web technologies, you’ll build towards mapping an application for insecurities, and understanding how to identify and mitigate threats.
- Access 64 lectures & 8 hours of content 24/7
- Map an app for insecurities using various tools & tricks, including Burp Suite
- Explore serious vulnerabilities like SQL injection, cross-site scripting, cross-site request forgery, XXE attacks, & more
- Find & hunt each vulnerability through the points developers use to secure the web app at the time of development
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: lifetime
- Access options: web streaming, mobile streaming
- Certification of completion not included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: all levels
Compatibility
- Internet required
THE EXPERT
Atul Tiwari has more than 7 years of working experience in the information security field. He has trained more than 3,000 students in information security and penetration testing. With his expertise in web application penetration testing, Atul has performed penetration tests, security audits, and security analysis for private enterprise, governments, and security agencies to assist with cyber threats.
KEY FEATURES
This course aims to teach you in-depth WiFi hacking and security. Upon completion, you’ll be confident in breaking all types of WiFi encryption methods. Starting as a complete beginner with little to no knowledge of WiFi security and Kali Linux, you’ll learn the most important elements of WiFi hacking so you can begin applying them to a career in ethical hacking.
- Access 118 lectures & 7 hours of content 24/7
- Get an introduction to Kali Linux & network basics
- Learn how to passively & actively gather information
- Identify vulnerabilities in a target
- Overrun buffer memory, perform password attacks, attack WiFi networks, & more
- Discuss client side & server side web vulnerabilities
- Test & exercise your defenses to ensure they’re up to task by simulating real-world attacks
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: lifetime
- Access options: web streaming, mobile streaming
- Certification of completion not included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: all levels
Compatibility
- Internet required
THE EXPERT
LearnPentest is a group of penetration testers and ethical hackers with an extensive background in web application security, web and software development, network administration and exploit development. They have over 7 years of professional experience in the cyber security domain. Their instructors hold some of the most valuable certifications in the cyber security domain including: OSCP, LPT, C|EH, CISSP, OSCE.
June 21, 2018 / by Marco / Bundle, Business', Certification, Computer, deals, design, entrepreneur, hacker, Professional, website

The Computer Hacker Professional Certification Bundle for $49

KEY FEATURES
To beat hackers, you have to think like them, and in this course you’ll master the skills of hacking and penetration in order to learn how to defeat malicious hackers. Companies of all sizes are constantly looking to improve IT security in this day and age, and this course will help you get qualified as an ethical hacker.
- Access 19 comprehensive modules 24/7
- Use enumeration to catalogue system resources & potential routes to breach
- Discuss automated tools for breaching security like Trojans, backdoors, viruses, worms, & DOS attacks
- Learn the role of social engineering in stealing confidential information
- Explore web-based attacks that can take online systems down
- Understand how wireless network security can be breached & how hackers avoid protective measures like IDS, firewalls & honeypots
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: 1 year
- Access options: web streaming, mobile streaming
- Certification of completion included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: all levels
- Free technical support available 24/5 via email, telephone & online chat
- Limit: 1 for you, unlimited as gifts
Compatibility
- Mac
- iPhone
- iPad
- Windows 7 or later
- Android
- Browsers: Internet Explorer 8 or later, Google Chrome, Safari 8 or later, Mozilla Firefox
- Browser settings need to be changed when using a Mac. Information found here.
THE EXPERT
Vizualcoaching is an institution of passionate and talented educationists who support over 300,000 students all over the world. The institution consists of over 180 individuals all specializing in their own aspects of combining education with technology.
For more details on this course and the instructors, click here.

KEY FEATURES
Certified Information Systems Security Professional (CISSP) is a globally recognized IT certification that covers subject matter in a variety of Information Security topics. Earning this certification will put you at the head of the pack in the IT field and allow you to work in a variety of fields, from network security to identity and access management.
- Access 10 comprehensive modules 24/7
- Learn about accounts & identity management
- Perform technical penetration testing & discuss layers of protection
- Explore connectivity interfaces & applications
- Apply integrity controls & learn different types of encryption
- Understand software OS & design
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: 1 year
- Access options: web streaming, mobile streaming
- Certification of completion included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: all levels
- Free technical support available 24/5 via email, telephone & online chat
- Limit: 1 for you, unlimited as gifts
Compatibility
- Mac
- iPhone
- iPad
- Windows 7 or later
- Android
- Browsers: Internet Explorer 8 or later, Google Chrome, Safari 8 or later, Mozilla Firefox
- Browser settings need to be changed when using a Mac. Information found here.
THE EXPERT
Vizualcoaching is an institution of passionate and talented educationists who support over 300,000 students all over the world. The institution consists of over 180 individuals all specializing in their own aspects of combining education with technology.
For more details on this course and the instructors, click here.

KEY FEATURES
Certified Information Systems Auditor (CISA) is a globally recognized designation for IS audit control, assurance, and security professionals. Earning this certification will put you at the head of the pack in the IT field and allow you to demand a higher salary in a variety of information security fields. It also may just be the first hurdle for scoring high-paying IT jobs in the first place.
- Access 7 comprehensive modules 24/7
- Learn about internal control classifications & IT strategy
- Discuss information systems maintenance practices & media disposal process
- Understand how to evaluate service level management practices
- Explore network security devices & network components
- Learn business continuity & disaster recovery regulations
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: 1 year
- Access options: web streaming, mobile streaming
- Certification of completion included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: all levels
- Free technical support available 24/5 via email, telephone & online chat
- Limit: 1 for you, unlimited as gifts
Compatibility
- Mac
- iPhone
- iPad
- Windows 7 or later
- Android
- Browsers: Internet Explorer 8 or later, Google Chrome, Safari 8 or later, Mozilla Firefox
- Browser settings need to be changed when using a Mac. Information found here.
THE EXPERT
Vizualcoaching is an institution of passionate and talented educationists who support over 300,000 students all over the world. The institution consists of over 180 individuals all specializing in their own aspects of combining education with technology.
For more details on this course and the instructors, click here.

KEY FEATURES
Certified Information Security Manager (CISM) is a globally recognized, advanced certification that validates individuals who have demonstrated the possess the knowledge and exeperience required to develop and manage an enterprise information security program. If you ever want to run IT at a company, this is an essential certification. Here, you’ll learn the technical prowess and business savvy to excel in an enterprise environment and earn a CISM certification.
- Access 6 comprehensive modules 24/7
- Learn about information security management
- Discuss risk assessment methodologies & implement an info risk assessment process
- Understand how to develop an information security strategy
- Integrate enterprise business objectives & info security policies
- Learn the security stakeholder education process
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: 1 year
- Access options: web streaming, mobile streaming
- Certification of completion included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: all levels
- Free technical support available 24/5 via email, telephone & online chat
- Limit: 1 for you, unlimited as gifts
Compatibility
- Mac
- iPhone
- iPad
- Windows 7 or later
- Android
- Browsers: Internet Explorer 8 or later, Google Chrome, Safari 8 or later, Mozilla Firefox
- Browser settings need to be changed when using a Mac. Information found here.
THE EXPERT
Vizualcoaching is an institution of passionate and talented educationists who support over 300,000 students all over the world. The institution consists of over 180 individuals all specializing in their own aspects of combining education with technology.
For more details on this course and the instructors, click here.

KEY FEATURES
In this course, you’ll learn about computer hacking forensics. Yes, sort of like what they do on CSI. This course begins with a look at the action required immediately after an attack has been identified, and then proceed to examine the in-depth procedures involved in investigating a hacking. If you have an interest in working on the legal side of computer hacking, this course is for you. Before you know it, you’ll be prepared to take and pass the CHFI certification exam.
- Access 22 comprehensive modules 24/7
- Learn how to carry out an investigation according to industry best practices & legal guidelines
- Cover searching & seizing resources as required for the investigation
- Know how to handle digital evidence to maintain legal standards
- Acquire & duplicate data to preserve evidence and facilitate further investigation
- Use Access Data’s Forensic Toolkit (FTK), EnCase & special steps to review data whilst leaving all evidence intact
- Understand steganography & how such techniques can be used to mask data theft
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: 1 year
- Access options: web streaming, mobile streaming
- Certification of completion included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: all levels
- Free technical support available 24/5 via email, telephone & online chat
- Limit: 1 for you, unlimited as gifts
Compatibility
- Mac
- iPhone
- iPad
- Windows 7 or later
- Android
- Browsers: Internet Explorer 8 or later, Google Chrome, Safari 8 or later, Mozilla Firefox
- Browser settings need to be changed when using a Mac. Information found here.
THE EXPERT
Vizualcoaching is an institution of passionate and talented educationists who support over 300,000 students all over the world. The institution consists of over 180 individuals all specializing in their own aspects of combining education with technology.
For more details on this course and the instructors, click here.

The Certified Ethical Hacker Bootcamp Bundle for $39

KEY FEATURES
Hackers are getting more sophisticated by the day, but so are their crime-fighting counterparts. Commonly known as ethical hackers, these cybersecurity experts leverage a hacker’s own tools against them, keeping networks—and the sensitive data they hold—safe. Featuring more than 75 hours of training, this collection of expert-led courses can help you take the fight online and certify your skills as a bona fide cybersecurity professional.
- Access 526 lessons & 77 hours of content 24/7
- Learn from industry experts in an interactive, lab-filled environment
- Foster skills in incident management, penetration testing & more
- Explore common threats, such as viruses, social engineering & DDoS attacks
- Understand the necessary steps to secure a system
- Prepare to ace the EC-Council Certified Ethical Hacker v9 exam upon completion
Included Courses:
- Introduction to Ethical Hacking
- Footprinting and Reconnaissance
- Scanning Networks
- Enumeration
- Malware Threats
- Sniffing
- Social Engineering
- Denial of Service
- System Hacking
- Session Hijacking
- Hacking Webservers
- Hacking Web Applications
- SQL Injection
- Hacking Wireless Networks
- Hacking Mobile Platforms
- Evading IDS, Firewalls, and Honeypots
- Cloud Computing
- Cryptography
- CEH – Test Prep Questions
PRODUCT SPECS
Details & Requirements
- Length of time users can access this content: 1 year
- Access options: web
- Certification of completion included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: all levels
Compatibility
- Internet required
THE EXPERT
CyberTraining 365 is the best training destination for you and your team. Here you can Master Cyber Security techniques such as Analyzing Malware, Penetration Testing, Advanced Persistent Threats, Threat Intelligence Research, Reverse Engineering, and much more.
The training courses are up-to-date on all the latest technologies and industry standards. All of this is offered at a great value in a self-paced online environment. CyberTraining 365 prepares you for industry-recognized certifications so you are fully prepared for the best job opportunities in the industry.
The Complete Raspberry Pi Hacker Bundle for $19
KEY FEATURES
The fun and possibilities are virtually limitless with a Raspberry Pi 3. That is, if you know what you’re doing. In this beginner-friendly course, you’ll learn everything you need to know to start using this popular Internet of Things (IoT) platform to its fullest.
- Access 76 lectures & 4.5 hours of content 24/7
- Work w/ Python, GPIO pins, & sensors
- Explore the Pi Camera Module
- Build an Amazon Echo Clone
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: lifetime
- Access options: web streaming, mobile streaming
- Certification of completion not included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: all levels
Compatibility
- Internet required
THE EXPERT
Lee Assam has over 18 years of programming, development and IT experience. He has a Bachelor’s degree in Electrical and Computer Engineering and a Master’s Degree in Computer Science.
Lee teaches at Universities on topics ranging from Software Development to Electrical Engineering and prototyping. He likes coming up with new ideas and prototyping them using the Arduino and Raspberry Pi platforms.
His passion and hobby is Arduino and the Internet of Things. He has been playing around with the Arduino and the Raspberry Pi platforms since their inception, and uses his Electrical Engineering background coupled with software development skills to create and develop exciting projects. Lee prefers a hands-on, project-based learning approach and uses his teaching background to make concepts fun and entertaining, while at the same time educational and informative.
KEY FEATURES
This course is an all-inclusive introduction to the Raspberry Pi platform. Catered for all levels, this project-based course will get you up and running with the basics of Pi, before escalating to full projects. Before you know it, you’ll be building a gaming system to play old Nintendo, Sega, and Playstation games and a personal digital assistant using the Google Assistant API. Now that’s progress.
- Access 50 lectures & 2 hours of content 24/7
- Understand all the components needed to get your Raspberry Pi up & running
- Learn how to easily prepare an SD card & flash it for any OS
- Work w/ GPIO pins & learn how to programmatically control them w/ Python
- Build simple circuits w/ an LED & a fully function gaming system w/ RetroPie
- Discuss the different types of Raspberry Pi models
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: lifetime
- Access options: web streaming, mobile streaming
- Certification of completion not included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: beginner
Compatibility
- Internet required
THE EXPERT
Lee Assam has over 18 years of programming, development and IT experience. He has a Bachelor’s degree in Electrical and Computer Engineering and a Master’s Degree in Computer Science.
Lee teaches at Universities on topics ranging from Software Development to Electrical Engineering and prototyping. He likes coming up with new ideas and prototyping them using the Arduino and Raspberry Pi platforms.
His passion and hobby is Arduino and the Internet of Things. He has been playing around with the Arduino and the Raspberry Pi platforms since their inception, and uses his Electrical Engineering background coupled with software development skills to create and develop exciting projects. Lee prefers a hands-on, project-based learning approach and uses his teaching background to make concepts fun and entertaining, while at the same time educational and informative.
KEY FEATURES
One of the ways to expand your Raspberry Pi horizons is by integrating it with other boards. In this course, you’ll learn how to set up a NodeMCU module a setup the latest firmware. Through this project-based course, you’ll harness the power of NodeMCU to code two different projects.
- Access 29 lectures & 1.5 hours of content 24/7
- Complete two projects using the Lua programming language
- Configure & use NodeMCU w/ Arduino IDE and program it using C++
- Execute animated graphics on the LCD
- Build a fully-functional web server to remotely control an AC appliance
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: lifetime
- Access options: web streaming, mobile streaming
- Certification of completion not included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: all levels
Compatibility
- Internet required
THE EXPERT
Comfiny is dedicated to creating a better e-learning experience for anyone who wants to explore the field of cutting-edge technologies. Their business idea supports this vision by offering a wide range of well-designed and high-quality courses.
They have a committed team of developers from various IT industries who are involved in sharing their knowledge and skill. The idea is to explore the cutting-edge technologies with minute details, covering every aspect and ensuring that the learning curve is easy for the beginner as well as advanced learners.
KEY FEATURES
The best way to learn Raspberry Pi is by doing and in this course, you’ll get familiar with specific features by building your own GPS tracking system. From setup and configuration to location tracking through Google Maps, this course will help you go from beginner to advanced with Raspberry Pi.
- Access 43 lectures & 2 hours of content 24/7
- Install the latest Raspbian OS without any external monitor
- Learn how to test whether the GPS module is functioning or not
- Discuss the Linux commands needed to access GPS functionality on the terminal
- Get to know about GPS data extraction & programming using Python
- Design a dashboard & analyze GPS data in real-time from anywhere
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: lifetime
- Access options: web streaming, mobile streaming
- Certification of completion not included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: all levels
Compatibility
- Internet required
THE EXPERT
Comfiny is dedicated to creating a better e-learning experience for anyone who wants to explore the field of cutting-edge technologies. Their business idea supports this vision by offering a wide range of well-designed and high-quality courses.
They have a committed team of developers from various IT industries who are involved in sharing their knowledge and skill. The idea is to explore the cutting-edge technologies with minute details, covering every aspect and ensuring that the learning curve is easy for the beginner as well as advanced learners.
iOS 11 Hacker eLearning Bundle – only $15!
EXPIRED: iOS 11 Hacker eLearning Bundle – only $15!
Expires: May 25, 2018, 11:59 pm EST

If you’re looking to create some genius applications for Apple’s newest operating system, iOS 11, then you’ve stumbled upon the right deal! The iOS 11 Hacker eLearning Bundle is packed with 150 hours of serious tips, tricks and tutorials to get you programming in iOS and MacOS. You’ll have lifetime access to all 8 courses and content so you can learn and build at your own pace.
Highlights:
- Learn how to build incredible iOS apps.
- 150 hours of invaluable content.
- 8 fabulous courses in 1 super-discounted deal:
- iOS 11 and Swift 4 Bootcamp Crash Course
- WatchOS Beginner Crash Course. Learn to code in Swift 3.0
- Introduction to SpriteKit
- Mastering Core Image: XCode’s Image Recognition and Processing Framework
- The Ultimate iOS 11 Course. Learn to Build Apps!
- The Complete MacOS Developer Course
- Complete iOS 11 Machine Learning Masterclass
- How to Make a Freaking iPhone App
- Unlock the secrets behind coding with Swift, Xcode, SpriteKit and more.
- Make any kind of app from practical games to image recognition features.
About the authors:
Yohann Taieb holds a BS in Computer Science from FIU University. He has been a College instructor for over 10 years, teaching iPhone Development, iOS 11, Apple Watch development, Swift 3, Unity 3D, Pixel Art, Photoshop for programmers, and Android.
Nick Walter is an iOS developer that has been focused on mobile app design and creation for over 3 years. His involvement in the iOS community started off with a bang, and in 2013 he was one of 25 students worldwide to be invited to Apple’s “Cocoa Camp.” Nick is also co-president of an Apple developer group called “Cocoa Heads.”
John Bura has been programming games since 1997 and teaching since 2002. John is the owner of the game development studio Mammoth Interactive. This company produces XBOX 360, iPhone, iPad, android, HTML 5, ad-games and more. Mammoth Interactive recently sold a game to Nickelodeon! To this day John has 40 commercial games that he has contributed to.
Sandy Ludosky is a freelance Web Designer and Developer based out of Toronto, in Ontario, Canada. She specializes in Front-End development with HTML, CSS, CSS3 Animation, Sass, Javascript, and JQuery.

Testimonials:
“Great course- shows you how to effectively build on top of prior knowledge. I’ve coded before, but never in iOS, so this is great for total beginners or people who haven’t coded in awhile and want to improve or learn a new environment. He breaks it down so Xcode doesn’t seem like a scary interface anymore.” – S. Hernandez
“Brilliant instructions. The lectures explaining functions and classes are super, and going through these I understand and are able to apply it safely in my own programming.” – Soren
Pricing:
Normally, this bundle of applications sells for $199 but for a limited time only, you can get all 8 iOS courses for only $15! That’s a monstrous savings of 92% off the regular price.
Click the BUY NOW button to start your training today!
Deal terms:
- You’ll receive a coupon code after completing your purchase, to register at the AcademyHacker website for lifetime access.
- All videos are streamable downloads and require an Internet connection for viewing. They are not downloadable.
The Professional Ethical Hacker Bundle for $49
DO YOU LIKE WHAT YOU’VE READ?Join our subscription list and receive our content right in your mailbox. If you like to receive some Great deals our Freebies then subscribe now! Name Email
read moreThe Computer Hacker Professional Certification Bundle for $49
DO YOU LIKE WHAT YOU’VE READ?Join our subscription list and receive our content right in your mailbox. If you like to receive some Great deals our Freebies then subscribe now! Name Email
read moreJanuary 12, 2018 / by Marco / Business', Cybersecurity, deals, design, entrepreneur, Ethical, hacker, subscription, Training, website, Yr

CyberSecurity Ethical Hacker Training: 1-Yr Subscription for $99

KEY FEATURES
The digital space is more crowded than ever yet the vast majority lack even basic cyber security skills. You can advance your skills, however, through this training, helping you to identify the gaps in your knowledge and proceed on a self-paced track to ultimately become a fully capable ethical hacker. You can learn anywhere, anytime, on any device and earn transcripts, certificates, and achievement recognition throughout. Not only will you become confident working with cybersecurity, but you just may be ready to pursue a career in this booming industry.
- Access a library of 663 courses, 313 quizzes, & over 150 hours of training
- Learn CompTIA Security+ & Network+, ECSA, CHFI, IPTA, & more
- Identify gaps in your knowledge w/ an adaptive skill measurement that gauges your proficiency
- Understand where to start on a learning path based on your test results
- Study at your own pace
- Participate & earn transcripts, certificates, & achievement badges
- Ask world class instructors questions whenever you need
PRODUCT SPECS
Details & Requirements
- Length of time users can access this course: 1 year
- Access options: web streaming & mobile streaming
- Certification of completion included
- Redemption deadline: redeem your code within 30 days of purchase
- Experience level required: all levels
- To browse the course catalog, click here
Compatibility
- Internet required
THE EXPERT
Social27 is the leader in online academies. They partner with the best trainers to produce relevant and up-to-date content that is delivered in a modern social learning platform.
For more details on this course and instructor, click here.
